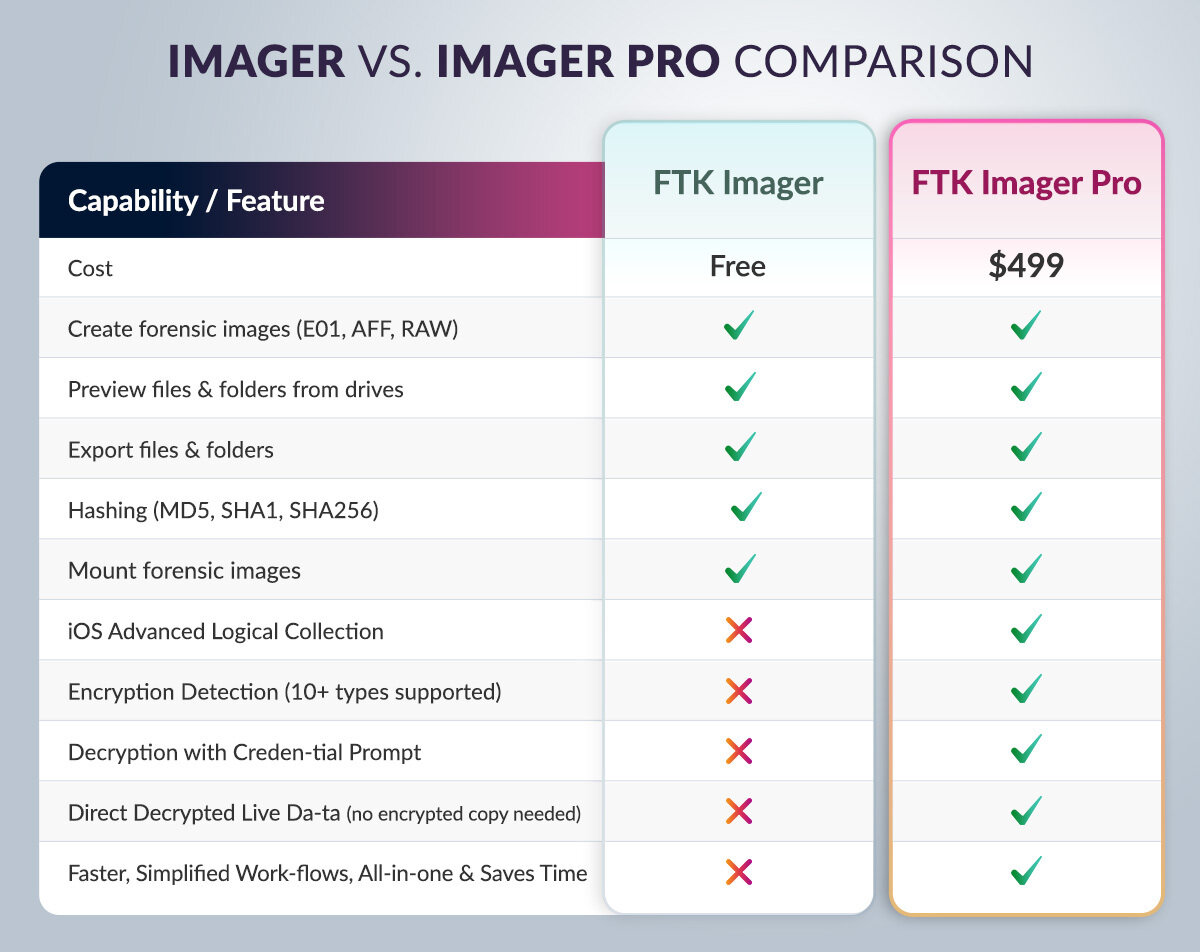
FTK Imager vs. FTK Imager Pro
Is Exterro FTK Imager Pro the Right Tool for You?
With FTK Imager Pro, you can:
Incident Response and DFIR Teams
Preview compromised systems, preserve volatile data, and create forensic images to support further analysis.
Law Enforcement and Digital Forensic Examiners
Conduct on-scene triage, verify whether evidence exists, and acquire drives using documented forensic imaging methods.
Corporate Security and HR Investigations
Assess devices discreetly to determine whether deeper forensic analysis is required.













.png)