Why Data Breach Investigations Are No Longer Optional
.jpg)
Data breaches used to be contained quietly, investigated over weeks, and disclosed cautiously. That operating model is gone.
Today, organizations are expected to prove what happened—quickly, accurately, and defensibly. Regulators demand it. Insurance carriers require it. Legal teams depend on it.
The shift is fundamental: Breach response is no longer about detection. It is about investigation under time pressure.
Let’s start with GDPR’s 72-Hour rule to make this real.
Where the 72-Hour Rule Came From—and Why It’s Breaking Teams
The modern breach response standard originates from the General Data Protection Regulation (GDPR), which requires organizations to notify regulators within 72 hours of becoming aware of a breach.
This wasn’t an arbitrary number. It was designed to:
- Force rapid transparency to regulators
- Prevent delayed disclosure that hides risk from consumers
- Ensure organizations actively investigate, not defer
The problem is not the rule itself. The problem is what it assumes:
That organizations can move from awareness → investigation → conclusion in 72 hours.
Most cannot.
Even in the U.S., where laws like the California Consumer Privacy Act (CCPA) vary by state, the direction is clear:
- Shorter notification timelines
- Greater specificity in disclosure
- Increasing penalties for incomplete or inaccurate reporting
Legislation is moving toward a simple expectation: If you report a breach, you must explain it—with evidence.
Cybersecurity Insurers Have Raised the Stakes
Cyber insurance providers have become one of the most important—and under-discussed—drivers of post-breach investigations.
Policies increasingly require:
- Formal forensic investigation reports
- Proof of scope and impact
- Evidence of containment and response actions
Without this:
- Claims can be reduced or denied
- Coverage disputes increase
- Future premiums rise significantly
From the insurer’s perspective, this is straightforward: If you cannot prove what happened, you represent uncontrolled risk.
This has created a second clock alongside regulation:
- Regulators demand notification
- Insurers demand validation
Both require the same thing: defensible evidence.
The Real Problem: Time vs. Evidence
Organizations are caught between two opposing forces:
- The need for speed (regulatory deadlines, executive pressure)
- The need for accuracy (legal defensibility, insurance validation)
Meanwhile, the environment has become more complex:
- Data is distributed across endpoints, SaaS platforms, and remote users
- Security tools generate alerts—but lack full investigative context
- Legal and compliance teams require chain-of-custody from the start
The result is a structural gap: Organizations are expected to produce verified answers faster than their systems are designed to support.
What Actually Happens in Most Breach Scenarios
When investigation capabilities don’t match expectations, organizations default to risk-heavy decisions:
- Over-reporting due to uncertainty
- Under-reporting that leads to later exposure
- Missed deadlines and regulatory penalties
- Findings that cannot be defended under scrutiny
In these situations, every decision—legal, technical, executive—is made without confidence.
A Retailer Responds to an Incident: Avoiding Unnecessary Notification
A national retail organization detected suspicious activity tied to a privileged account. Security tools flagged potential access but could not confirm exposure.
With the 72-hour window approaching, legal needed a decision.
The organization initiated a targeted investigation:
- Remote collection from the affected endpoint
- Analysis of user activity within a defined timeframe
- Preservation of evidence for legal review
Outcome:
- No sensitive customer data was exfiltrated
- Breach notification was avoided
- Regulatory and reputational risk were eliminated
Without investigation, they would have reported unnecessarily.
A Financial Services Organization Suspects Data Exfiltration: Confirming a Breach—and Reducing Its Scope
A financial services organization identified anomalous access to a shared repository containing customer data. Initial indicators suggested a large-scale breach—potentially requiring notification to the full customer base.
Instead of assuming a worst-case scenario – think Equifax:
- They collected endpoint and access data tied to specific users
- Analyzed file access and movement patterns
- Correlated activity across systems and timeframes
Outcome:
- Only a limited subset of records was accessed
- Notification scope was significantly reduced
- Reporting was precise, defensible, and aligned with regulatory expectations
Without investigation, they would have over-reported—at significant potential cost in fines, legal fees and brand damage.
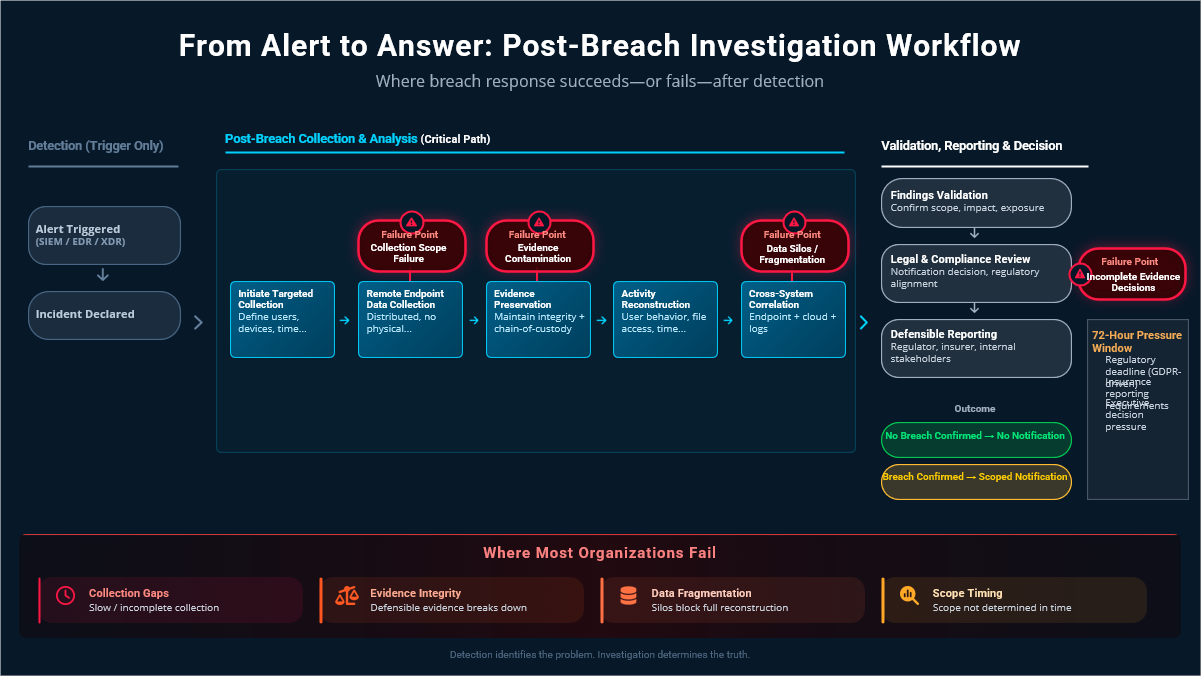
The Breach Investigation Workflow
The gap is not a lack of tools—it’s a lack of workflow. Organizations that succeed follow a consistent model:
Alert → Collection → Analysis → Validation → Reporting
- Alert: Detection systems identify suspicious activity
- Collection: Endpoint and system data is gathered quickly and remotely
- Analysis: Activity is reconstructed across users, devices, and timelines
- Validation: Findings are verified and preserved with chain-of-custody
- Reporting: Defensible conclusions are delivered to legal, regulators, and insurers
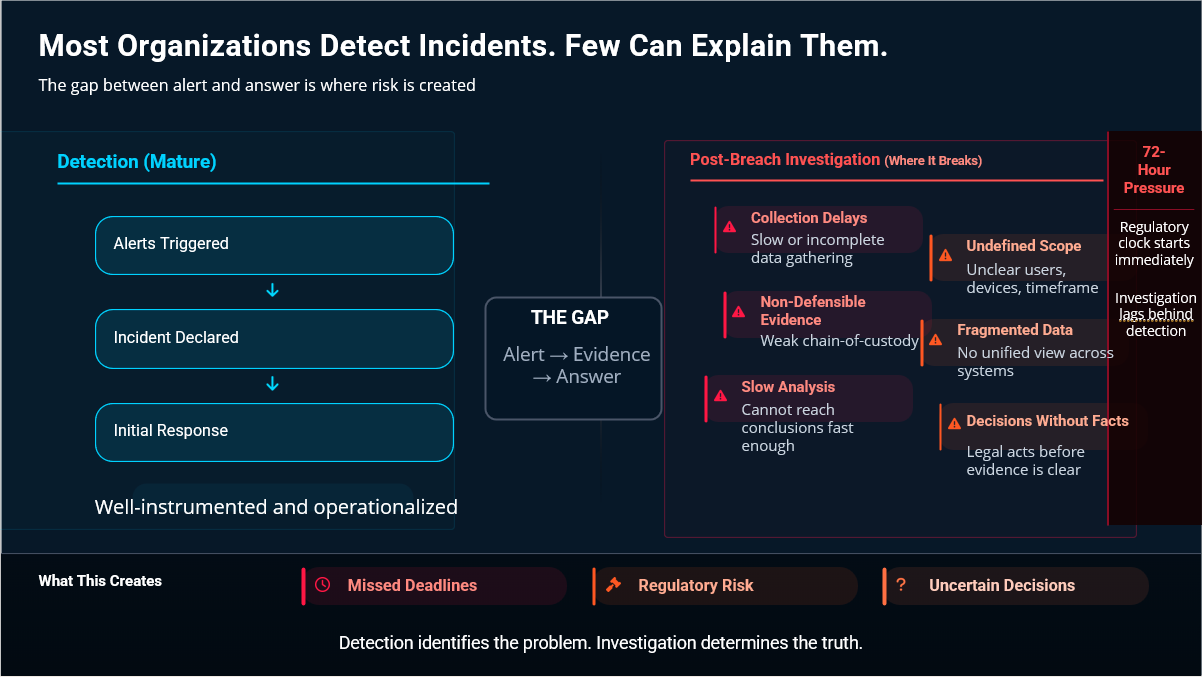
Most Organizations Are Strong at Detection. They Struggle with Everything That Follows.
Most enterprises have invested heavily in detection. Alerts fire. Incidents are declared. But that’s where maturity often ends.
Where Things Start to Break Down
Organizations are prepared to detect incidents. They are not prepared to explain them.
1. Collection Is Slow or Incomplete
Data cannot be gathered quickly across endpoints and environments, creating immediate delays.
2. Scope Is Undefined Early
Teams lack clarity on users, devices, and timeframe, leading to inefficient or missed collection.
3. Evidence Is Not Defensible
Chain-of-custody and preservation processes are inconsistent, putting findings at risk.
4. Data Is Fragmented
Information lives across systems and cannot be easily correlated into a full picture.
5. Analysis Takes Too Long
Teams struggle to move from raw data to conclusions within required timelines.
6. Decisions Are Made Without Facts
Legal and compliance are forced to act before the investigation is complete.
Why Evidence Matters More Than Alerts
Detection tools tell you something happened. Investigations determine what actually happened.
To meet regulatory and insurance expectations, organizations must:
- Collect data rapidly across distributed environments
- Preserve evidence without alteration
- Analyze activity in context—not isolation
- Produce defensible findings
This is not a security workflow. It is an investigative workflow.
What Tools Made This Possible
Organizations that execute effectively share a common capability set:
- Remote, scalable endpoint evidence collection
- Targeted acquisition based on users, timeframes, and activity
- Built-in chain-of-custody and auditability
- Integrated workflows from alert to reporting
These are not “nice to have” features.
They are what make modern breach response possible.
Where is Incident and Breach Notification Headed?
The directions are clear:
- Faster notification timelines
- Greater demand for accuracy
- Increased regulatory enforcement
- Stricter insurance requirements
The expectation is evolving from: “We experienced a breach” to “Here is exactly what happened, who was impacted, and why.”
Organizations that cannot meet this standard will face:
- Regulatory penalties
- Insurance challenges
- Legal exposure
- Loss of trust
Closing the Gap: From Alerts to Answers
Most organizations already have detection capabilities.
What they lack is the ability to turn alerts into answers—quickly and defensibly.
This is where an investigation-led approach matters.
Platforms like Exterro FTK Connect and Exterro FTK Enterprise are designed to support this exact workflow:
- Rapid remote collection from endpoints
- Immediate transition from alert to evidence
- Scalable analysis across systems and users
- Defensible reporting aligned to legal and regulatory requirements
Not as standalone tools—but as part of a unified investigative process.
Final Thought
Breach response has changed. It is no longer enough to detect an incident. You must explain it. And you must do it under pressure, with evidence, and within strict timelines.
Organizations that adapt will operate with control. Those that don’t will continue to react under uncertainty. The difference comes down to one capability: The ability to move from alert → evidence → answer.
To learn more about how to prepare for the inevitable--data breaches--download our whitepaper Before It Breaks: The Data Risk and Breach Mitigation Checklist.


