Why Many Smaller Police Agencies Are Unable to Perform Mobile Phone Forensics — And What Actually Works
A Conversation with Frank Mazzola, Mississippi Cyber Initiative Digital Forensics Analyst/ Lead Technician
Recently, I sat down with Frank Mazzola, who through the MS Cyber Initiative supports dozens of law enforcement agencies across several regions of Mississippi and is a member of the Mississippi Attorney General’s Cyber Fraud Task Force, focusing on digital forensic investigations. I expected a discussion of features and software comparisons.
What I got instead was a reality check about how investigations actually work.
And more importantly, how they often don’t.
Because the truth is, most digital investigations are not large federal cybercrime cases. They’re messy, time-sensitive situations handled by officers who need answers immediately.
Many Small Agencies are unable to Do Mobile Forensics because of costs.
One of the first things Frank explained was that many agencies are challenged with training their investigators on complex mobile forensic solutions and may be unable to invest on the initial cost of many of the high-end technologies and industry certifications.
They can try to get free resources and training through programs like NCFI or NW3C.
Thus, between purchase costs, certifications, storage, and training time, tools often sit unused or require shipping devices to regional labs.
He told me clearly:
“Lots of agencies can’t afford the major forensic phone tools or the certifications that go with them. So, they leverage programs such as the MS Cyber Initiative Forensics lab for assistance with preserving, extracting, and analyzing data..”
A delay can happen without access to the right equipment and resources.
A detective may have a victim, a suspect, or a witness sitting in front of them. But the phone, the single most important source of evidence, has to leave the scene and wait in a queue.
In addition, Frank also pointed out a second reason agencies don’t do extractions themselves: training/certification gaps. He described how some investigators won’t pursue even free certifications unless there’s an instructor-led class, which keeps dependence on regional labs in place. Certifications for most mobile forensic tools are expensive.
Operational Impact on Agencies
What this really creates is not just a technical gap — it creates an investigative bottleneck. When devices must be sent to a regional lab, investigators may wait days or weeks before knowing whether a case has any evidence. During that time, suspects remain uncharged, victims lose confidence, and officers move on to other cases.
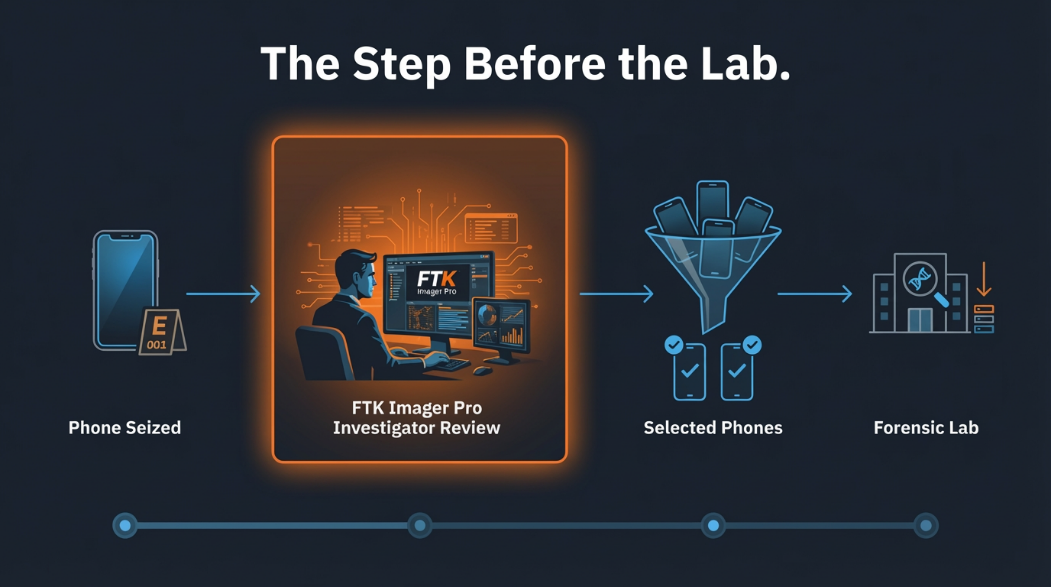
In practice, the first delay in a case is often not analysis — it is simply determining whether usable evidence exists. A triage-level collection changes that timeline from weeks to the same day.
Some Cases Don’t Require a Full Extraction
The digital forensics industry tends to operate under an assumption:
Every phone requires a full forensic acquisition.
Frank disagrees.
He described a real investigative workflow I’ve now heard from multiple agencies:
A detective interviews a victim in a stalking or harassment case, for example. The evidence they need is text messages. Not deleted partitions. Not a full device reconstruction. Just the conversation.
Frank explained: “Officers think they need a full file system extraction every time, which is often incorrect. Sometimes a logical extraction is all you need.”
Then he described what happens when they can do it on scene. The investigator starts the extraction and conducts the interview; when the interview ends, the data is ready.
“By the time the interview is done, they already have the messages (with a logical extraction). They can give the person their phone back.”
That single point matters more than most feature lists ever will.
Because returning a victim’s phone immediately isn’t just a convenience. It’s cooperation. I still believe a full file-system extraction should be performed on a suspect’s device.
That said, Frank emphasized this isn’t just about speed — it’s about proportionality. He described misdemeanor / witness / victim scenarios where a logical extraction is appropriate and contrasted that with cases where investigators default to “full file system” out of habit rather than necessity.
The Real Role of Triage
Digital forensics has quietly developed a missing middle.
Full lab forensic examination.
On the other:
No examination at all.
What Frank described is the space in between — triage.
“Sometimes investigators just need to know if further investigation is necessary.”
That sentence explains the value of a preview capability better than any technical specification. In many cases, the goal isn’t to complete the investigation immediately.
It’s to determine:
Is there evidence here worth escalating?
If yes → send to lab.
If no → close quickly and move on.
This is where tools like Imager Pro actually change workflow, not just analysis.
Why Investigators Still Trust FTK-Based Collection
Frank has been working in digital forensics since 2010. He’s seen the industry evolve from early computer forensics to today’s mobile-centric investigations.
Yet one theme kept repeating. Reliability.
He explained why investigators keep returning to FTK collection tools even when they use other analysis platforms:
“ When I image with FTK Imager it, I know the image hashing and validation of the E01 is already done.”
He also emphasized something courts care deeply about — verification.
Modern software parses artifacts automatically, but he doesn’t rely solely on automation.
“If I find something important, I drill down to the artifact and validate it. It makes for stronger testimony in court.”
That matters. Because software output is evidence only when the examiner can explain it.
Further, Frank was very direct about this: he likes automation, but he does not “take things at face value.” He described finding the source artifact, confirming it in another viewer/tool, and treating it as court-relevant only then, especially for “smoking gun” items.
Defensibility Matters More Than Automation
One point Frank emphasized repeatedly was courtroom testimony. Automated parsing tools are valuable, but they don’t replace an examiner’s ability to explain how evidence was located and verified.
By drilling down to the underlying artifact and validating it with a second method, the examiner can testify not only to what the software reported, but also to how the data were confirmed. That distinction matters in court, where the examiner's credibility — not the software—determines whether evidence is trusted.
In other words, collection and validation procedures are often more legally important than advanced analytics.
The Everyday Reality of Investigations
Frank gave examples that perfectly illustrate what digital forensics actually looks like outside conferences and vendor demos.
He recovers deleted crime scene photos from SD cards. He retrieves accidentally deleted files for officers. He validates artifacts across multiple tools.
And most of the time, agencies don’t ask him to interpret evidence — they ask him to collect it.
“About 80% of my work is just pulling the data and documenting the extraction.”
They want the portable reports quickly and to review them themselves, 20% of investigators give me a scope and evidence to look for and validate the answers for their cases. This does take more time.
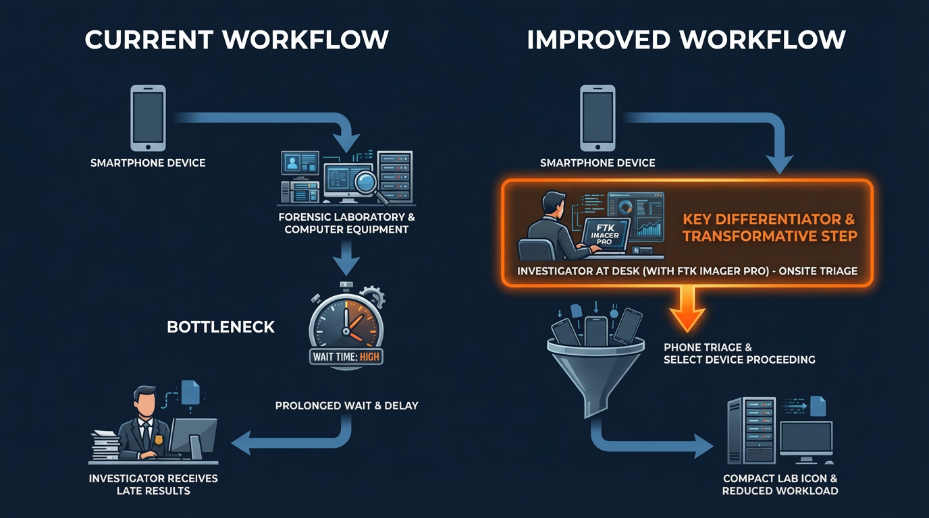
This is a crucial insight. The bottleneck in investigations today is not just analysis.
It’s also collection.
Frank described why that 20% is different: “I’m not a mind reader.” When detectives sit with him and give scope (what they’re looking for), he’ll help navigate artifacts, validate them, and testify to both the extraction and the findings. Without that scope, they just want extraction + documentation.
Consider a stalking complaint. A victim reports threatening messages but cannot give up their phone for several days because it contains work contacts and family communication. Without a quick extraction option, investigators may have no evidence to act on. With a logical extraction performed during the interview, the messages are preserved immediately, and the phone is returned. The investigation can move forward the same day.
Why Lightweight Tools Matter
Here is where Imager Pro fits into Frank's real workflow. Not as a replacement for advanced forensic systems. But as an access point to them.
He explained it simply:
“You can put it on a laptop and use it in the field. You don’t have to take every phone back to the lab.”
Sometimes, a Logical Extraction of an iPhone is enough.
Sometimes you just need a write blocker and FTK Imager on a laptop to get an E01 of a small flash drive or SD Card. Maybe do a preview of a drive in FTK Imager to see if there's any easily recoverable deleted evidence to export.
If you know where specific artifacts are, you can drill down to them with FTK Imager and quickly export them for examination with open-source tools.
In other words:
Imager Pro doesn’t replace full forensic analysis. It helps investigators decide whether they need it. And that is a difficult problem to solve in practice.
Frank also compared this to other free tools that are useful for extraction, but not for drill-down/verification. His point: collection is only half the job; the ability to quickly drill down and validate (possibly parse), is what makes a lightweight field workflow actually useful.
The Gap FTK Imager Pro Solves
Digital evidence is now present in almost every investigation, but trained forensic examiners are in short supply.
The industry has been trying to solve this with automation.
What Frank’s experience shows is that the real solution is workflow.
Investigators need:
- Quick collection or a method of preserving the evidence
- Immediate preview
- Decision support (You may not have an expert in your department, but having a contact to assist you via phone can help)
- Some type of training if they are going to review data on their own.
Not every case needs a lab. But every case needs a decision.
Frank gave a concrete example of how process + tooling comes together in the real world: he said they run FTK Imager Pro in an automation pipeline (via a CLI version) alongside other tools, so evidence can be collected, processed, and handed off into analysis workflows with minimal friction.
Final Thought & Key Takeaways
After the interview, what stood out most wasn’t a feature, a competitor comparison, or even a technology discussion.
The message Frank communicated was also about courtroom defensibility: validating with multiple methods/tools may take longer, but it creates stronger testimony—because the examiner can explain both the “what” and the “how,” not just present a tool-generated
The bottom line was this:
Digital forensics is no longer about extracting everything in many, if not most, cases.
It’s about determining what matters.
And sometimes the most valuable capability in an investigation isn’t deep analysis — it’s knowing quickly whether deeper analysis is necessary at all.
That’s the gap many agencies live in today. And based on how investigators like Frank actually work, it’s exactly where triage-focused tools belong.
What this conversation reinforced for me is that the biggest challenge in digital forensics isn’t a lack of tools — it’s a mismatch between real investigative workflows and how forensic technology is typically used.
Investigators aren’t working in labs with unlimited time and training. They’re making decisions during interviews, at scenes, and under time pressure. The first question usually isn’t “Can we reconstruct the entire device?” — it’s “Is there evidence here that justifies the next step?”
Frank’s experience shows that access to evidence is often more important than depth of analysis. Many agencies don’t need a full forensic examination at the start. They need a reliable way to preserve, preview, and decide whether to escalate. When they have that, cases move faster, victims cooperate, and limited forensic resources are used where they matter most.
Full forensic analysis will always be necessary for serious cases. But modern investigations require an intermediate step — a defensible triage process.
Ultimately, the value of a collection tool is not just what it analyzes, but what decisions it enables. Sometimes the most important outcome isn’t performing a deep forensic investigation — it’s confidently determining whether one is needed at all.
For many agencies, the question is no longer whether they can perform full digital forensics — it is whether they can make timely investigative decisions. Triage collection is what enables that.
Learn more about how FTK Imager Pro can help you with field triage on iOS devices.
