A Review of the Zero Trust Framework
There is no doubt that the Cyber landscape of today has become very complicated, compounded because of the COVID-19 pandemic. One of the biggest issues today has to deal with the remote workforce.
One of the key security threats is that of commingling the home network with the business network, which results in a huge uptick of compromised credentials. Although Virtual Private Networks (VPNs) have proven their worth to protect usernames and passwords, they too have started to reach their breaking points.
So what can be done? Many businesses around the world are starting to adopt a new concept known as the Zero Trust Framework, the focal point of this article.
Shutterstock
What Is the Zero Trust Framework?
A technical definition follows:
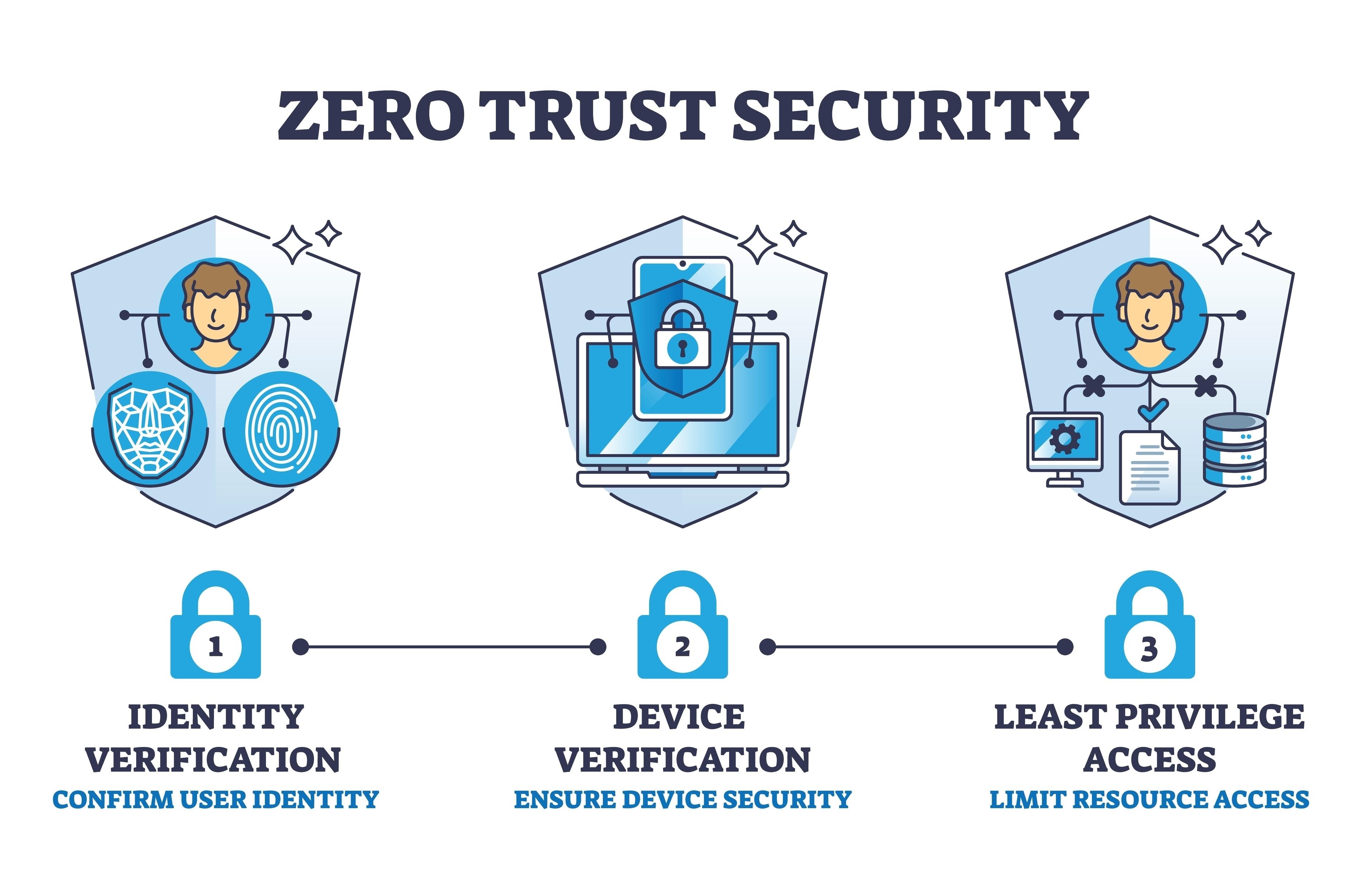
“Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network. Regardless of where the request originates or what resource it accesses, Zero Trust teaches us to ‘never trust, always verify.’ Every access request is fully authenticated, authorized, and encrypted before granting access.”<sup>1</sup>
Based on the above, a few assumptions can be made about the Zero Trust Framework (also called “Model”):
- It makes the assumption that absolutely nobody, from either the inside or outside of your business, can be trusted;
- It already assumes that a Cyberattack is underway;
- Anybody who wants to gain access to anything, especially to shared resources, has to be fully authenticated through at least three or more layers of authentication.
Because of this, the Zero Trust Framework is often viewed as extreme. But in today’s environment, nothing can be taken for granted, even employees that have been with you for a very long time.
What Is Impacted by It
Besides employees, there are also key components within your business that have to be put under the scrutiny of the Zero Trust Framework. These include the following:
All sorts of devicesThis includes everything from hardwired servers to workstations and all forms of wireless devices. You want to make sure that only legitimate devices are accessing your network infrastructure and not rogue ones, such as employees using their personal smartphones to access shared resources.
Software applicationsWith a majority of your employees now working from home, it is even more difficult to tell than ever before if they are using legitimate applications that have been authorized by your IT Security team. In this regard, you need to confirm that any applications trying to access your servers are the real thing.
Your dataIt is the data that you store, use, and collect on a daily basis that literally forms the lifeblood of your business. This includes everything from your Intellectual Property (IP) all the way to the Personal Identifiable Information (PII) datasets of your employees and customers. You do not want anything to fall into the hands of a Cyberattacker. It is absolutely imperative that only legitimate people gain access to this data, which explains the need for many layers of authentication to take place first.
Your overall infrastructureMany people associate the Zero Trust Framework with just the digital component of your business. But it includes the physical infrastructure as well. If an individual needs to gain access to a server in your data center, they should be completely vetted first. This includes going through at least three layers of authentication, for instance, a smart card, entering a unique ID number, and submitting to a biometric modality such as fingerprint and/or iris recognition.
Your network infrastructureGaining access to a network line of communications and moving laterally from there is one of the most common ways the Cyberattacker uses to break through your lines of defense. Therefore, not only do you need to make sure that all possible vulnerabilities are remediated, but also that only legitimate employees can initiate a path of network communications.
As the Zero Trust Framework mandates, your remote workforce should be given only those rights and permissions they need to perform their daily job functions, which is referred to as the “Concept of Least Privilege.” The Framework further establishes that your network infrastructure should be divided into smaller segments, which are known as “Subnets.” Therefore, if the Cyberattacker breaks through one layer of authentication, the statistical odds that they will break through the others become greatly diminished.
The Advantages of the Zero Trust Framework
There are a number of strategic advantages to it, which are:
- You are exposed to a lesser degree of vulnerability: By assuming nobody can be trusted, you are actually decreasing the threat surface for the Cyberattacker to penetrate. To a certain degree, you are also at a much-lowered level of risk of an insider attack from precipitating.
- You will have a varied mix of authentication mechanisms: Using more than one layer of authentication does not mean that you use different forms of it. The Zero Trust Framework mandates that you utilize entirely different mechanisms, which was alluded to earlier in this article.
- Other areas of your business will also be segmented: Apart from your network infrastructure, there will be other aspects that will have to be further divided, such as the data that you store. For instance, rather than storing it all in just one on-premises database, you will have to contain it in different ones. In this scenario, you may even want to use a cloud-based platform such as AWS or Azure.
Conclusions
Overall, this article has examined what the Zero Trust Framework is. A future one will address how you can deploy it specifically to your business.
Sources<sup>1</sup>Microsoft Zero Trust Security



